In a new public statement released Wednesday, Swedish authorities have formally attributed a 2023 cyberattack targeting a critical western Swedish heating plant to a pro-Russian faction with direct ties to Russia’s national intelligence and security apparatus. This official designation marks the first time Sweden has publicly acknowledged the breach, and it aligns with a growing cascade of warnings from other European nations that Moscow is systematically targeting continental critical infrastructure.
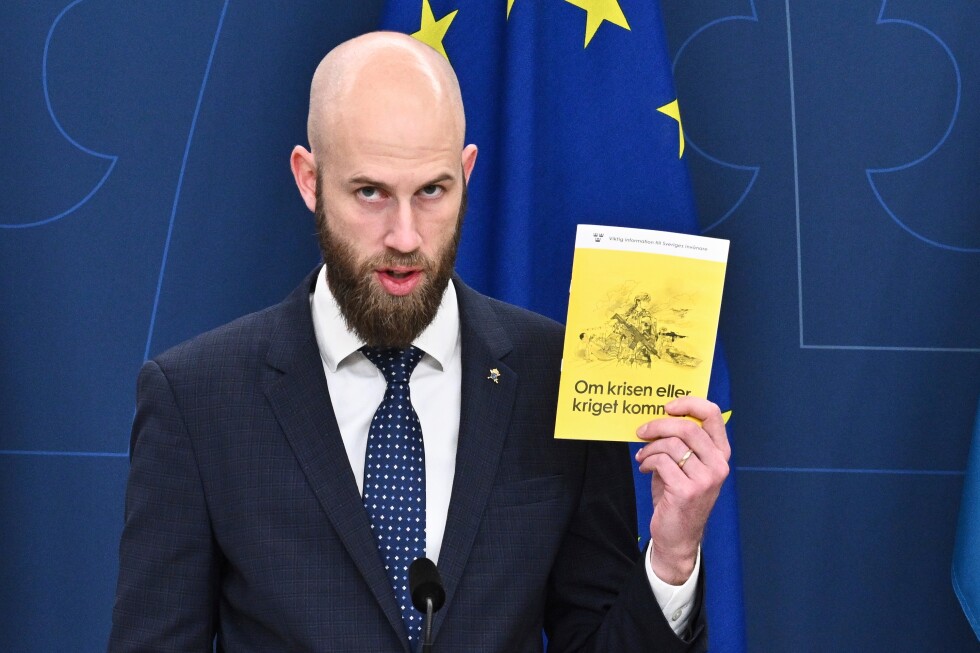
Carl-Oskar Bohlin, Sweden’s Minister for Civil Defense, confirmed in the announcement that the attempt to compromise the heating plant’s operations ultimately failed, though he declined to share additional specific details about the incident or the facility involved. Bohlin drew a direct parallel between the Swedish attack and coordinated cyber intrusions that hit Polish energy infrastructure in December 2023. Those Polish attacks disrupted services at combined heat and power facilities that serve nearly 500,000 residential and commercial customers, alongside targeting wind and solar energy generation sites. Following the incident, Polish investigators concluded that the hackers responsible held direct connections to Russian state intelligence services.
Bohlin emphasized that cross-border cyber operations targeting the control systems of European critical infrastructure, including both the Swedish and Polish incidents, pose severe, tangible risks to the stability of European societies. He characterized the sustained campaign of intrusions as evidence of reckless, high-risk behavior by Russian-linked actors that threatens everyday life across the continent.
This string of attacks is not an isolated trend. An Associated Press investigation has tracked more than 150 separate incidents of sabotage and hostile malign activity across Europe since Russia launched its full-scale invasion of Ukraine in February 2022, all of which Western officials have linked to Moscow. Western intelligence and security assessments outline that the core strategic goals of this campaign are threefold: to erode public support for Ukraine among European populations, sow widespread fear and social division across the continent, and divert law enforcement and investigative resources away from other pressing priorities.
The Kremlin has repeatedly and categorically denied allegations that it oversees any campaign of sabotage or hostile cyber activity across European territory.
In the months leading up to Sweden’s announcement, other European capitals have already flagged similar Russian-linked attacks on their own critical infrastructure. In December 2023, Danish authorities disclosed that 2024 cyberattacks carried out by Russian actors against a national water utility left hundreds of residential properties without running water. In August 2023, Norwegian police confirmed that pro-Russian hackers remotely exploited a vulnerability to open a flood valve on one of the country’s dams, triggering uncontrolled water discharge. Earlier last year, Latvia’s State Security Service reported that arson attacks targeting train cars and railway infrastructure were carried out by operatives acting on behalf of Russian interests.
This report was contributed by Ciobanu, reporting from Warsaw, Poland.